Security and access management is more critical than ever. We’ve just added support for Role-Based Access Control (RBAC) which allows you to manage users’ access to Bytesafe Firewalls, Registries and Repositories.
By applying the principle of least privilege, you can now limit who is allowed to do what action in your Bytesafe Workspace using both built-in and custom roles.
Why Role-Based Access Control is great for security-aware organizations? Read more to learn about a few example use cases.
When organizations grow it’s often advisable or required to grant users the ability to access features and packages based on their responsibilities. With role-based access control you’re able to manage things like:
- Make sure that only the security team can release packages quarantined by a firewall
- Limit which users can add new packages to registries
- Give users from other teams read-only access to a registry
- Delegate access control for certain registries to specific teams
Getting started with Role-Based Access Control in your Workspace
The more fine-grained access management is now available in our Business and Enterprise plans. A good start is to review your team members to make sure everyone has proper assigned roles and then on a registry or source repository level grant access what roles are allowed to perform various actions.
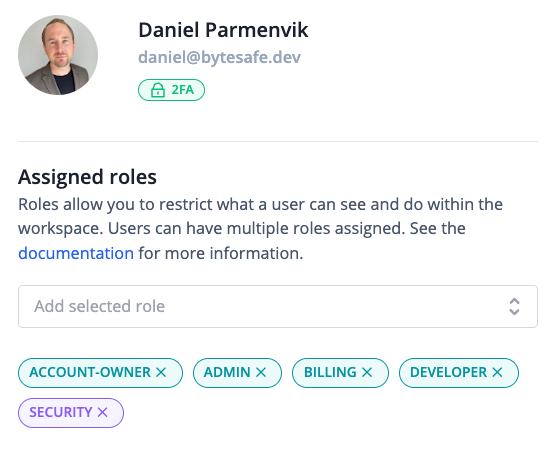
1. Review user assigned roles
Log in to your workspace and click on Teams in the navigation sidebar. Each team member has at least one role assigned. Simply click on the Edit button to make changes to assigned roles.
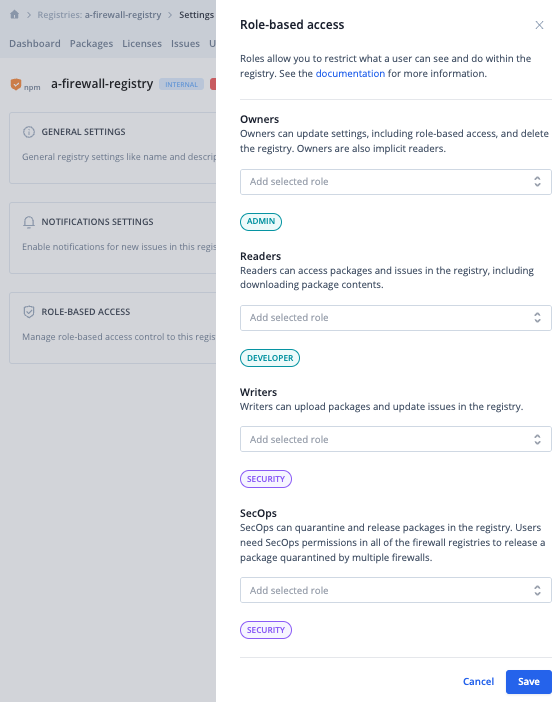
2. Review role-based access to existing registries or source repositories
Go to your Registry or Source repository, click on Settings and then on the Edit button under the section Role-Based Access.
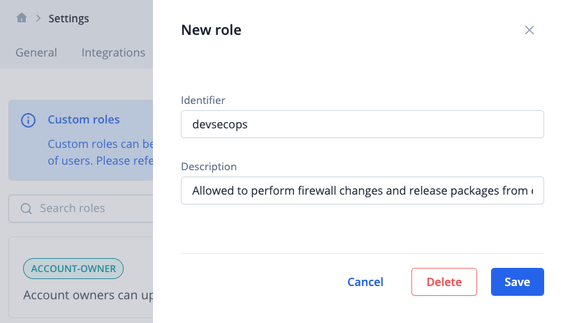
3. Add new custom roles (optional)
To add new custom roles on Workspace-level you click on Settings in the menu and then User Roles where you can add or edit existing custom roles.
Want to know more about Role-Based Access Control in Bytesafe?
Read more in our documentation on how to use Role-Based Access Control in your Workspace.
