The Bytesafe Solution
Take control of your package management


Software Composition Analysis
Identify open source software composition directly from your Git repositories

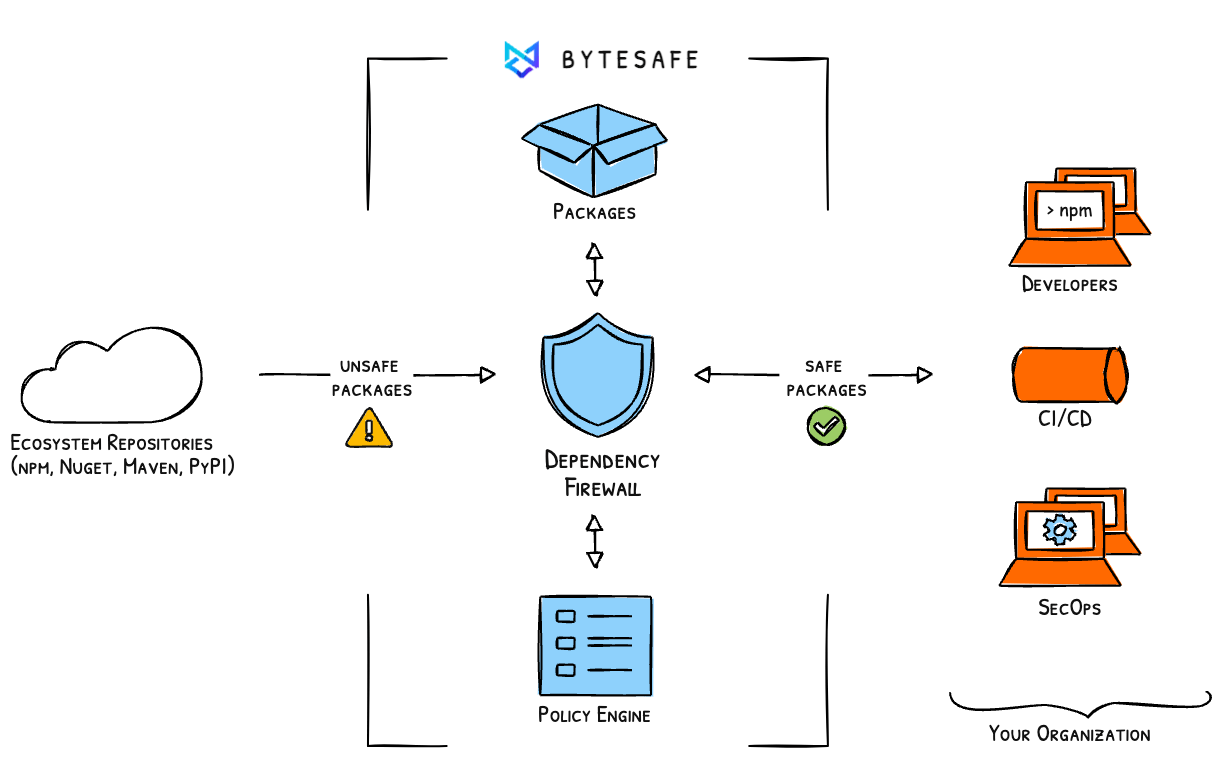
Dependency Firewall
Automatically quarantine vulnerable components from entering your supply chain

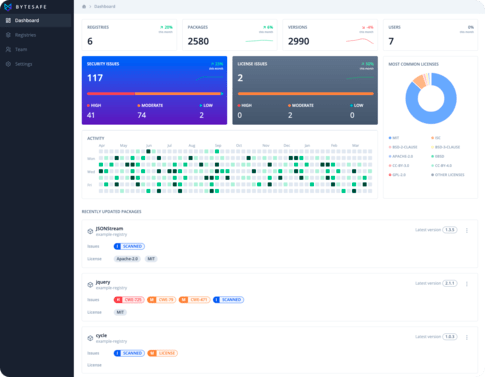
Vulnerability & License Scanning
Continuously scan and monitor your dependencies. Get notified of any issues

Issue tracking & Remediation
Identify issues, get notified & take action. Keep track every step of the way
Firewall for dependencies
Discover bytesafe
Secure by default private registries
Security built-in to the workflow
Combine your need for package management with security. Add public dependencies and share private packages using your regular tools.
Create a trusted source for every stage of your software development lifecycle (SDLC). A source where packages are continuously monitored and secured.
Automatic quarantine of malicious packages
Block undesirable components before they can put your business at risk. Quarantined packages are held securely within Bytesafe - notifying you of issues early.
With customizable thresholds - to stay in control without breaking builds.
Protection from Dependency Confusion
Bytesafe secures your supply chain from dependency confusion attacks by default!
New versions of internal packages are prevented from being fetched from external sources. All while maintaining full access to external registries for public packages!
Know the dependencies you are using
Identify what packages your apps depend on and their dependents. Use Bytesafe as the team’s secure source of truth for npm and maven packages.
Security is a team effort. So information is made available for all team members, from relevant metrics to advisory details.
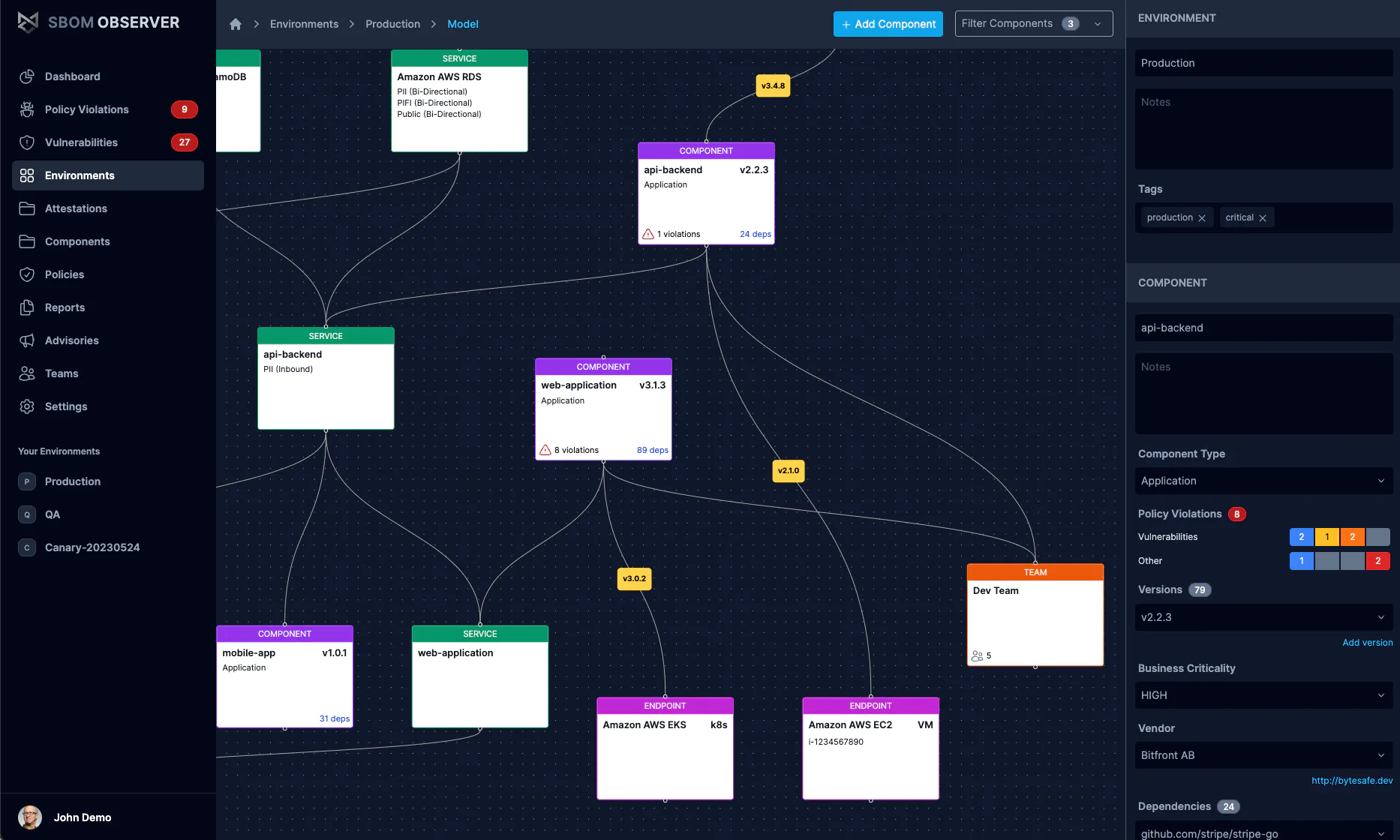
Track risk. Enforce policy. Prove compliance.
Go beyond SBOM generation with SBOM Observer— a platform built for SBOM-centric workflows from ingestion to reporting.
Enforce policies automatically, monitor vendor and internal risk in one view, and produce regulator-ready proof on demand for customers and auditors alike.
The Bytesafe platform
Central hub to control your dependencies
By Developers for Developers
Work using your regular tools

Continue using regular npm and maven clients for both Developers and CI/CD. Using Bytesafe as a trusted source for private and public packages, instead of relying directly on the public registries. All added packages are continuously monitored for issues and vulnerabilities - both now and in the future.
Integrations
Bytesafe integrates with the services you use









open source is everywhere
Are you in control of the packages your applications are using?

Testimonials
What our clients say about us

"We use Bytesafe in our CI/CD pipeline to keep our Javascript packages secure. Setting up Bytesafe to use in combination with the regular public registries was super easy. It helps us share our internal private packages securely and efficiently across all our development teams."

"We create NodeJS & Java libraries and use Bytesafe in our CI/CD environment. For us it’s a very useful and important tool. Bytesafe has high availability which is crucial when installing packages in our projects. I want to highlight that the service keeps private packages secure. The dependency firewall keeps us safe and informed of potential vulnerabilities where we need to take action. Excellent tool!"