Supported ecosystems
What is a Dependency Firewall?
You define the rules: block packages with known CVEs, block known malicious packages or delay newly published versions for a configurable period to give the ecosystem time to surface zero-day threats before they reach you.
Works in front of enterprise repositories like JFrog Artifactory, Sonatype Nexus and similar. No agent installs. No workflow changes.

Everything included. No add-ons. No usage fees.
Key Capabilities
Policy Engine
Rules by package name, version range, age, source, license, and custom criteria. Block or log-only, with time-limited exceptions. Re-evaluated on every request.
Vulnerability Blocking
Block packages with known CVEs before install. Filter by CVSS and EPSS severity per registry or team. New advisories take effect immediately.
Malware Scanning
Detect malicious payloads, suspicious install hooks, and obfuscated code before execution. Quarantined packages are logged, never silently dropped.
Provenance Verification
Verify packages were built by expected publishers using Sigstore and SLSA attestations. Detect pipeline swaps and version downgrades early.
Dependency Confusion
Block namespace attacks where public packages impersonate your internal ones. Configurable upstream priority rules ensure private packages always win.
Package Observations
Every package is fingerprinted: first-seen date, download frequency, requester, version age. New or unusual patterns are flagged automatically.
Audit Logging
Every block, allow, and exception is recorded and exportable to your SIEM. Built to make security teams and auditors happy, out of the box.
Dashboard & Metrics
Real-time security posture across all registries. See what's blocked and why, which teams trigger the most flags, and how exposure trends over time.
Publish Scanning
Packages are scanned for malware, secrets and sensitive data before they are published to an upstream registry.
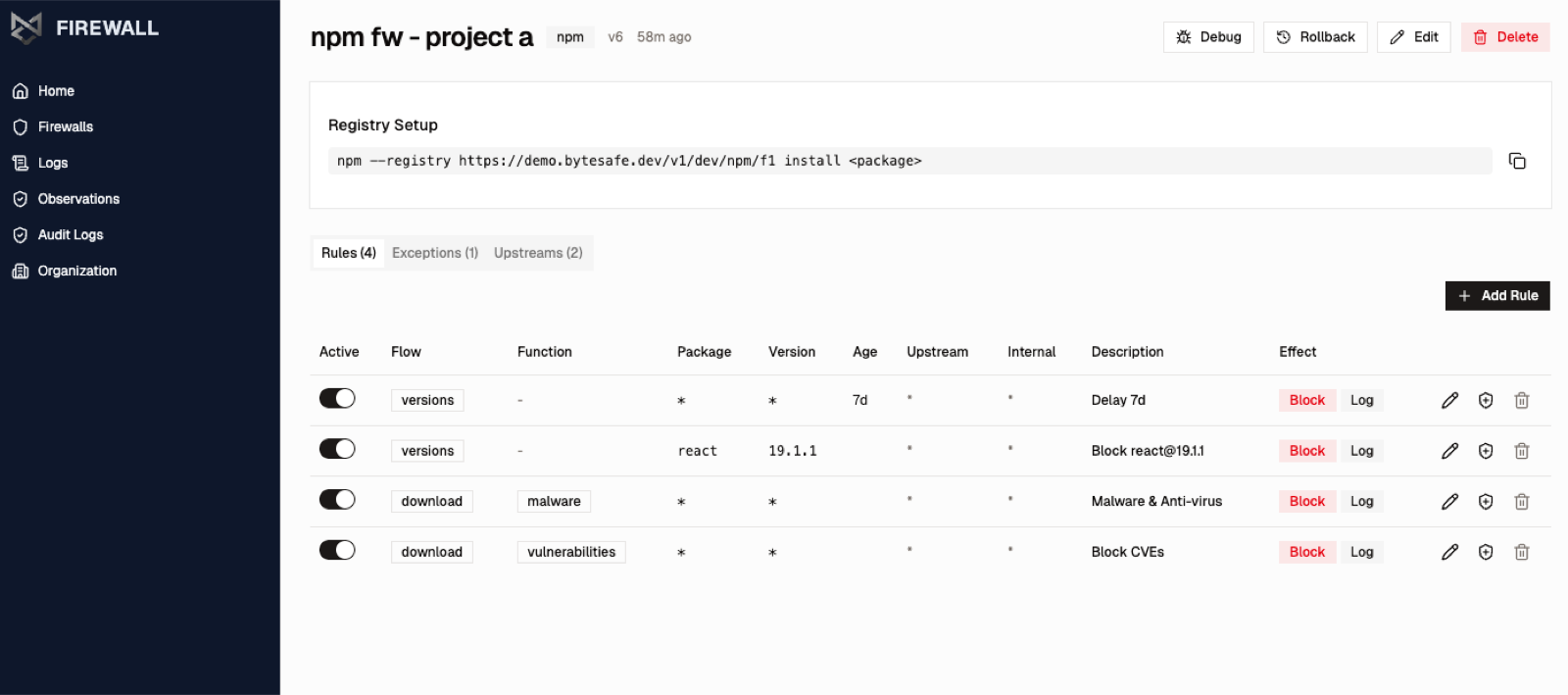
Firewall Rules
Define exactly what gets through and what doesn't
Each rule targets an ecosystem and applies a condition: vulnerability severity, package age, license type or name pattern. Rules either block or log. Stack multiple rules per firewall. Changes take effect immediately.
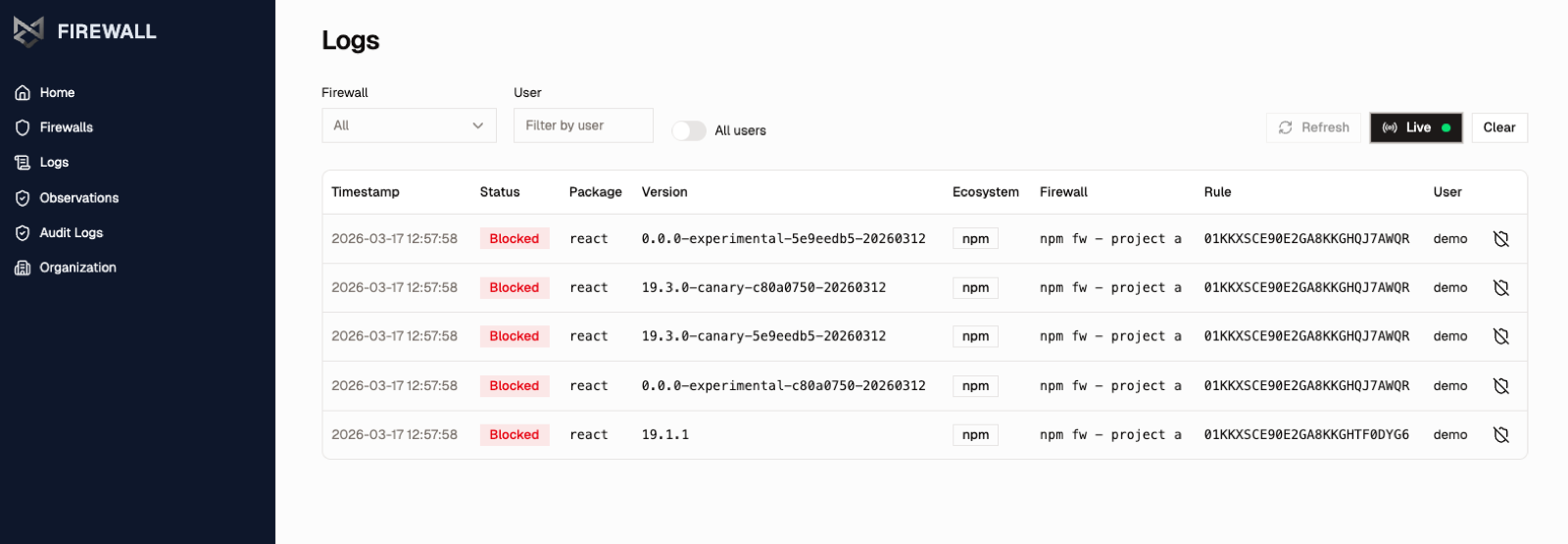
Live Firewall Logs
See what's happening per firewall and per user, in real time
Every blocked package is logged: package name, version, status, ecosystem, which firewall evaluated it, which rule triggered, and who requested it. Filter by firewall or user. Tail live during incidents or CI/CD runs.
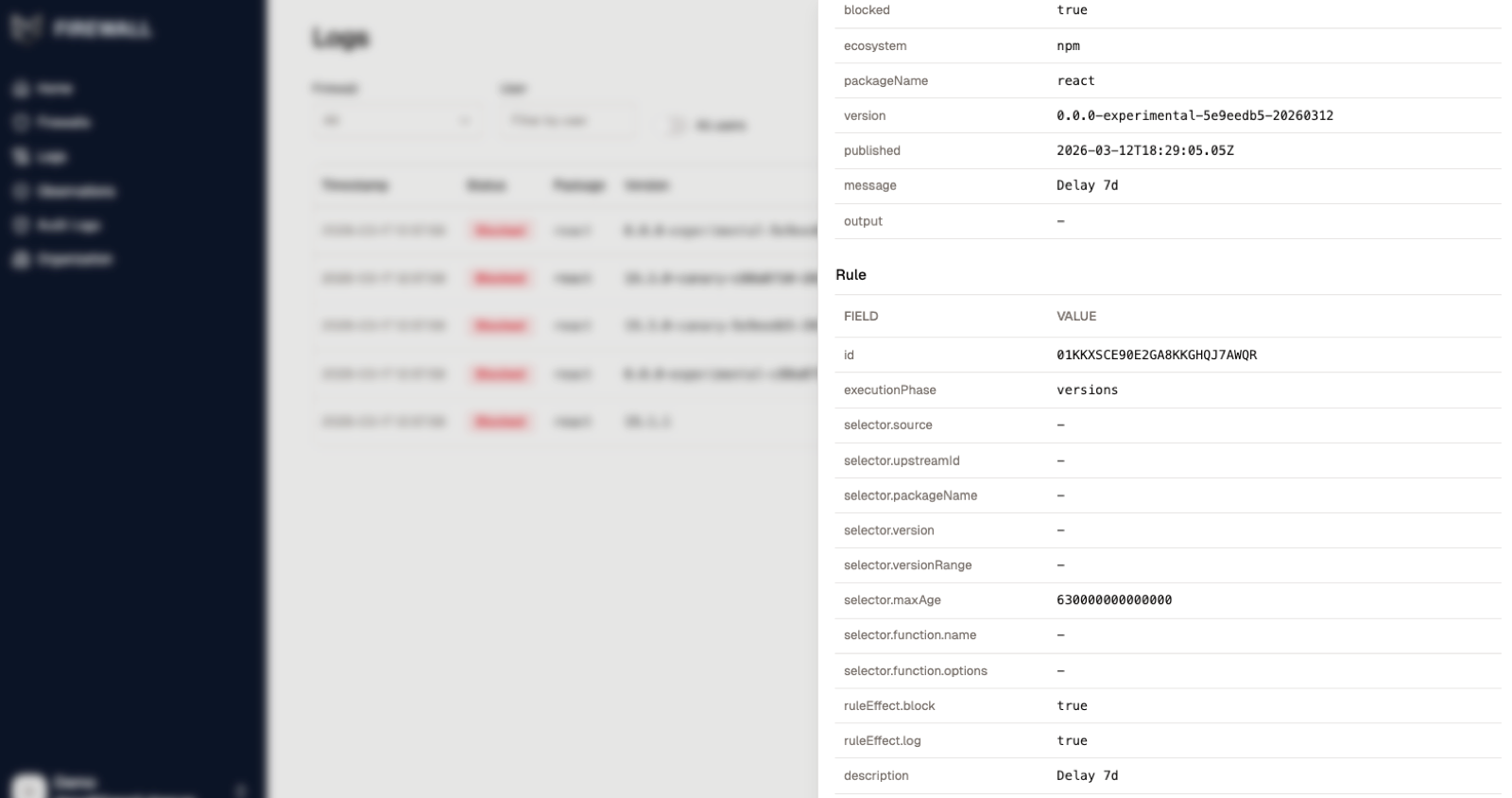
Block Reason Details
Know exactly why every package was blocked
Every blocked package shows full context: ecosystem, version, publish date, the rule that triggered, and whether the effect is block, log, or both. No guesswork for developers or security teams.
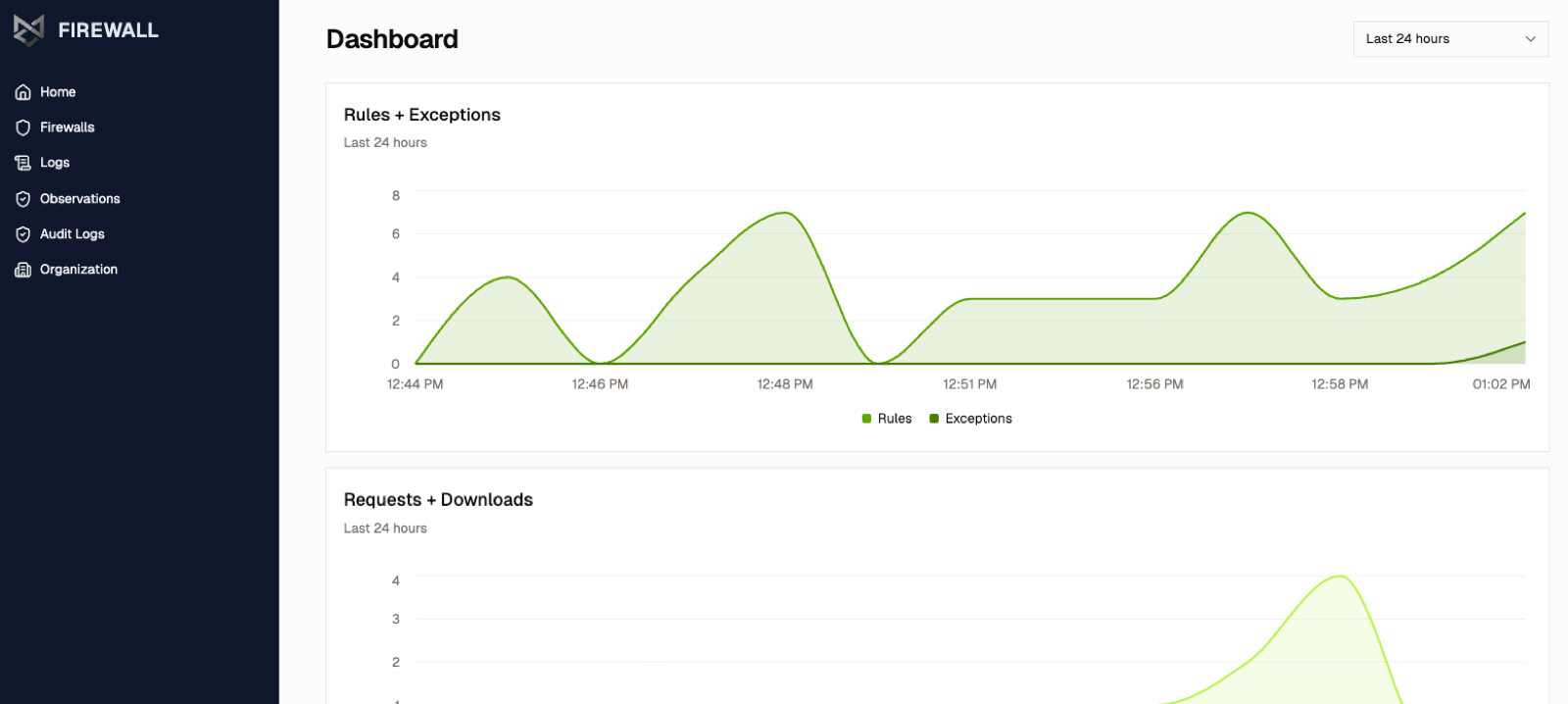
Security Dashboard
Track your security posture across all firewalls
Monitor rules triggered, exceptions granted, and package requests over time. See which firewalls are most active, spot trends, and verify your policies are working as expected.
Transparent protection in three steps
How It Works
A security layer between the public internet and your package repository. Your developers and pipelines notice nothing.
Route package requests through Bytesafe
Instead of pulling public packages directly without oversight, point your CI/CD pipelines and developer tooling at Bytesafe. Every package request passes through the firewall before reaching your environment.
Define your security policies
Set vulnerability thresholds, enable malware scanning, configure safety delays for new versions, and write allowlist/blocklist rules. Create multiple firewalls with individual rules to comply with different requirements across your organization.
Bad packages are blocked. Safe ones flow through.
Every request is evaluated in real time. Blocked packages is logged with the policy that triggered. Approved packages are served transparently.
Works with the repositories you already use